“On 2FA and MFA protected systems, after the password is entered, additional checks are then performed, often using one of the following technologies…”
Downloading
Authentication, 2FA, and MFA Rapid Reference
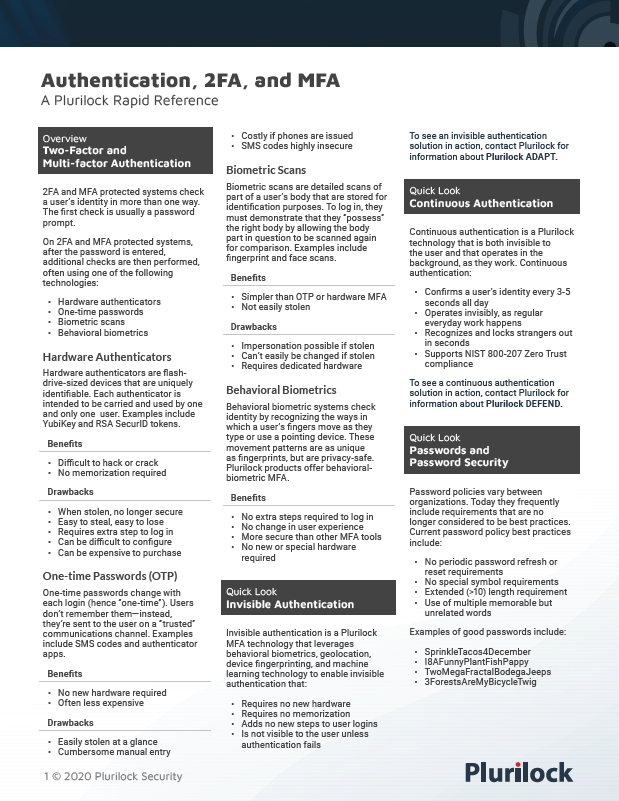
Concise rapid reference to 2FA, MFA, password best practices, and authentication vocabulary.

