Plurilock™ Tearsheets
Learn more about Plurilock products and services.
Plurilock Services Tearsheets
Automated compliance evidence generation with continuous controls monitoring across all major regulatory frameworks.
Continuous threat exposure management with automated breach simulation and incident readiness.
Comprehensive evaluation of AI governance posture with structured recommendations for safe, strategic AI growth.
Comprehensive application, API, and integration testing across your full technology stack under real-world attack conditions.
Guided Cloud Access Security Broker implementation with unified visibility and consistent policy enforcement.
Complete implementation-ready governance foundation with policies, standards, roles, and workflows for secure cloud adoption.
Automated policy enforcement with real-time compliance monitoring and proactive violation prevention across multi-cloud environments.
Comprehensive cloud security assessment, compliance validation, and cost optimization analysis across multi-cloud environments.
Managed data protection service combining DLP and insider threat capabilities as a service.
Advanced data protection architectures and engineering to safeguard your data against evolving threats.
Cross-functional rapid response teams providing immediate expertise for urgent IT and cybersecurity threats.
Continuous, adaptive identity and access management that protects against internal and external threats.
CIS-aligned baseline hardening for Azure and AWS with automated enforcement, continuous monitoring, and operational playbooks.
Comprehensive industrial control system security testing designed for operational environments where uptime is critical.
Always-on, proactive security approach that identifies, tests, tracks and mitigates dangerous vulnerabilities before exploitation.
Advanced PKI modernization and cryptography consulting services for enterprise security transformation.
Purple team collaboration with real-time feedback to simulate post-compromise attacker behavior across hybrid environments.
Comprehensive SOC operations, support, staffing, automation, and modernization services led by senior experts.
Advanced social engineering attack simulation including deepfakes, MFA bypass, and privilege escalation testing.
Comprehensive zero trust program evaluation with structured recommendations across all critical security domains.
Guidance and Recommendations
Sample, shareable addition for employee handbook or company policy library to provide governance for employee AI use.
Generative AI is exploding, but workplace governance is lagging. Use this whitepaper to help implement guardrails.
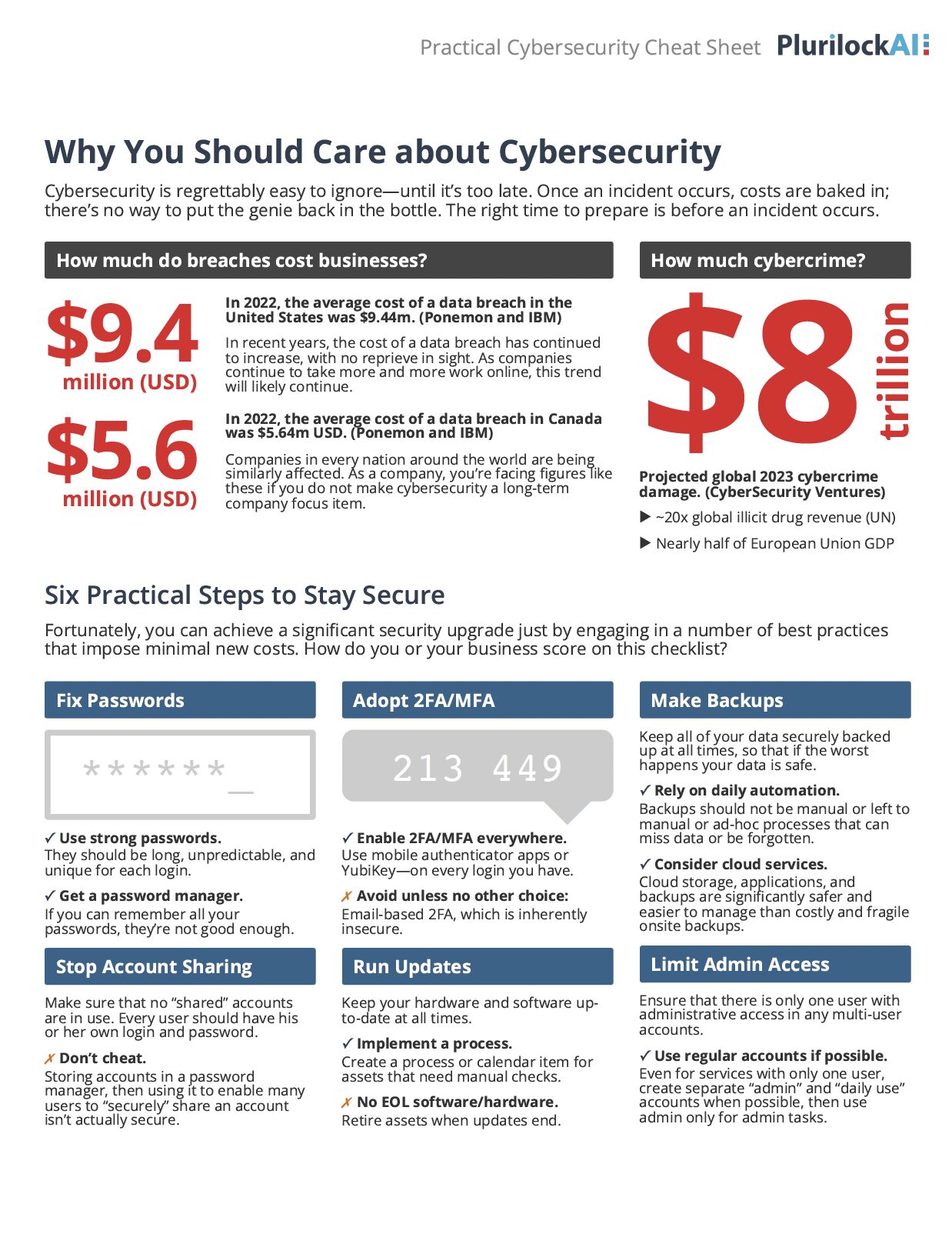
Cheat sheet for basics to stay secure, their ideal deployment order, and steps to take in case of a breach.