Vendor and Third Party Security Training in Utah
Comprehensive Third Party Risk Management Training for Utah Businesses
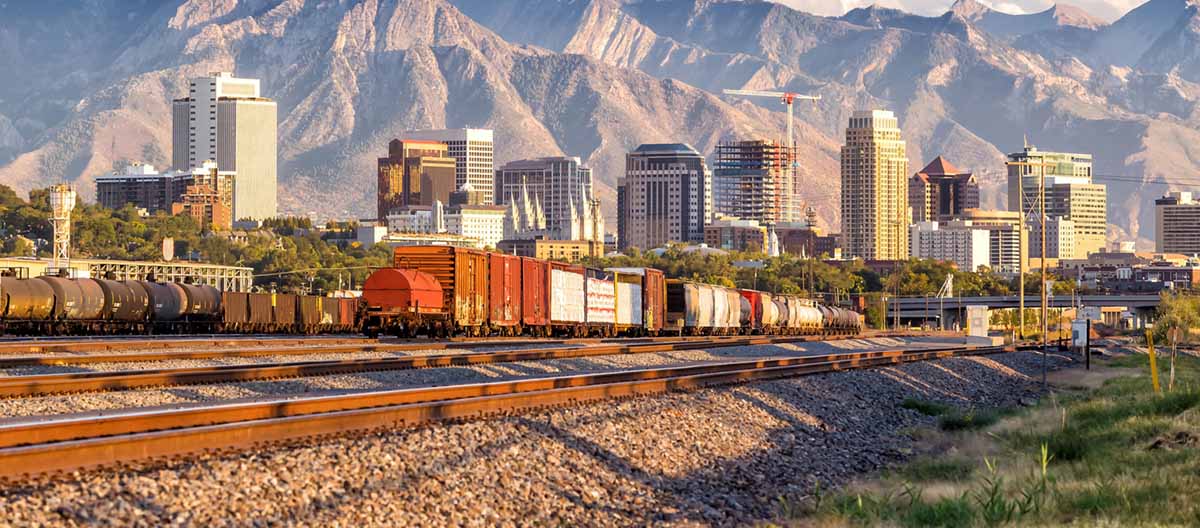
In today's interconnected business landscape across the Silicon Slopes and Wasatch Front, organizations face increasing cybersecurity risks from their vendor relationships and supply chain partnerships. Our specialized training programs help Utah companies develop robust third-party risk management capabilities, ensuring your team can effectively assess, monitor, and manage vendor security risks while maintaining compliance with industry regulations.
- Customized training solutions for manufacturing, construction, and technology sector supply chains
- BioHive partnership-focused security awareness programs
- Industry-specific vendor assessment methodologies for Utah's growing business ecosystem
- Practical frameworks for ongoing third-party risk monitoring and management
Supply Chain Security Training for Wasatch Front Industries
The diverse manufacturing and technology landscape along the Wasatch Front requires specialized attention to supply chain security. Our training programs address the unique challenges faced by local industries, from Tech Ridge technology firms to traditional manufacturers, helping organizations build resilient supply chain security practices that protect critical assets and maintain operational integrity.
- Manufacturing-specific supply chain risk assessment methodologies
- Security protocols for Tech Ridge technology partnerships
- Integration of cybersecurity best practices into existing procurement processes
- Risk mitigation strategies for complex supply chain networks
Contractor Security Awareness for Utah Construction Projects
The booming construction industry in Utah presents unique cybersecurity challenges when managing contractor relationships. Our specialized training programs help construction firms implement effective security protocols for contractor management, ensuring project data remains protected while maintaining efficient operations across multiple stakeholders.
- Construction-specific digital security protocols and procedures
- Contractor vetting and access management best practices
- Project data protection strategies for multi-contractor environments
- Security awareness training for temporary workforce management
Vendor Due Diligence Training for Salt Lake Chamber Members
Working closely with organizations throughout the Salt Lake Chamber network, our vendor due diligence training programs help businesses establish effective security assessment protocols. These programs are designed to protect your organization while fostering strong business relationships across the Intermountain region's growing economic ecosystem.
- Comprehensive vendor security assessment frameworks
- Risk-based approach to vendor qualification and monitoring
- Integration of cybersecurity requirements into procurement processes
- Ongoing vendor relationship management best practices
Business Partner Security Training for Utah's Tech Sector
As Utah's technology sector continues to expand, particularly around Silicon Slopes and Tech Ridge, maintaining secure business partnerships becomes increasingly critical. Our training programs help technology companies implement effective security measures across their partner networks while supporting rapid growth and innovation.
- Technology partnership security assessment methodologies
- Data protection protocols for collaborative development environments
- Security requirements for strategic technology alliances
- Risk management strategies for technology ecosystem partnerships
Specialized Training for BioHive and Healthcare Partnerships
Utah's thriving BioHive ecosystem requires particular attention to third-party security in healthcare and life sciences partnerships. Our specialized training programs address the unique compliance requirements and security challenges faced by organizations operating in these sensitive sectors.
- Healthcare-specific vendor security compliance training
- BioHive partnership security assessment protocols
- Regulatory compliance integration for healthcare vendors
- Security frameworks for sensitive research partnerships