AI Agents With Full Computer Access: Security Implications Most Organizations Aren’t Ready For
The AI agent era isn’t a future state anymore. It’s arriving now. Over the past several months, the major AI labs have been racing to ship autonomous computer-control capabilities. OpenAI
AI Agents With Full Computer Access: Security Implications Most Organizations Aren’t Ready For
The AI agent era isn’t a future state anymore. It’s arriving now. Over the past several months, the major AI labs have been racing to ship autonomous computer-control capabilities. OpenAI
AI Agents With Full Computer Access: Security Implications Most Organizations Aren’t Ready For
The AI agent era isn’t a future state anymore. It’s arriving now. Over the past several months, the major AI labs have been racing to ship autonomous computer-control capabilities. OpenAI
Previous

Why the Best Security Programs Start With Adversary Simulation
There’s a persistent belief in enterprise security that if you check enough boxes, you’ll be safe. It’s comforting. It’s orderly.

Red Team vs. Purple Team: Which Does Your Organization Actually Need?
There’s a question that comes up constantly in conversations with security leaders: “Should we run a red team engagement or

How to Build a Cyber Risk Quantification Program That Actually Informs Business Decisions
There’s a dirty secret in cybersecurity governance: most cyber risk quantification (CRQ) programs fail to deliver on their promise. Not

When OT Meets the Parking Lot: Why Vehicle Cybersecurity Can’t Be Ignored
We tend to think of cybersecurity in terms of servers, endpoints, and cloud environments. But there’s a class of networked

AI Won’t Replace Cybersecurity—But It Will Replace Cybersecurity That Ignores AI
When Anthropic’s Claude Cowork capabilities spooked the broader software sector in late January and early February 2026, cybersecurity stocks got

The $1 Trillion Software Selloff and What It Means for Cybersecurity
In early February 2026, US software stocks shed roughly $1 trillion in market value over the course of a single

Early 2026’s Breach Disclosures Reveal the Real Cost of Data at Scale
Sometimes a single breach dominates headlines for weeks. Other times, several disclosures land in rapid succession, and the cumulative picture
Your LLM Infrastructure Is Already on Attacker Target Lists
If you’re running large language models in production, you need to understand something uncomfortable: you’re probably already on someone’s list.

CISOs Are Now Chief Resilience Officers, Leading Companies Through the AI Security Paradox
The boardroom conversation has changed. When executives discuss artificial intelligence in 2026, they’re not asking whether to adopt it—they’re demanding
IAM Automation Is Fraught, But Increasingly Necessary. Here’s How to Approach It.
Identity and access management (IAM) has reached a curious inflection point. On one hand, the sheer scale of modern enterprise

ICS and OT Systems are Becoming More Frequent Cyber Attack Targets
The term “cyber attack” brings ransomware and stolen data to mind, but today there’s a quieter yet equally devastating war

Identity-Focused Attacks Are a Trend—Here’s How They Work and What To Do About Them
In today’s digital landscape, a single set of valid employee credentials can be all an attacker needs to infiltrate an

Cybersecurity Awareness Month 2024 Provides Four Simple Steps to Secure Our World
In today’s technology-driven world, Cybersecurity Awareness Month serves as an important reminder of the proactive steps we can all take

Uncovering Hidden Threats: The Crucial Role of Penetration Testing in Cybersecurity
In the digital age, where data breaches and cyberattacks are increasingly common, safeguarding your organization’s digital assets isn’t just an

Plurilock Critical Services Mobilizes Rapidly—and This Transforms Outcomes
Cyber threats are evolving faster than ever. From sophisticated ransomware attacks to state-sponsored espionage, the speed at which an organization

How Many Vendors Are Represented In Your Environments?
Our Critical Services team routinely encounters environments populated by multiple products from multiple vendors and multiple VARs or suppliers. In
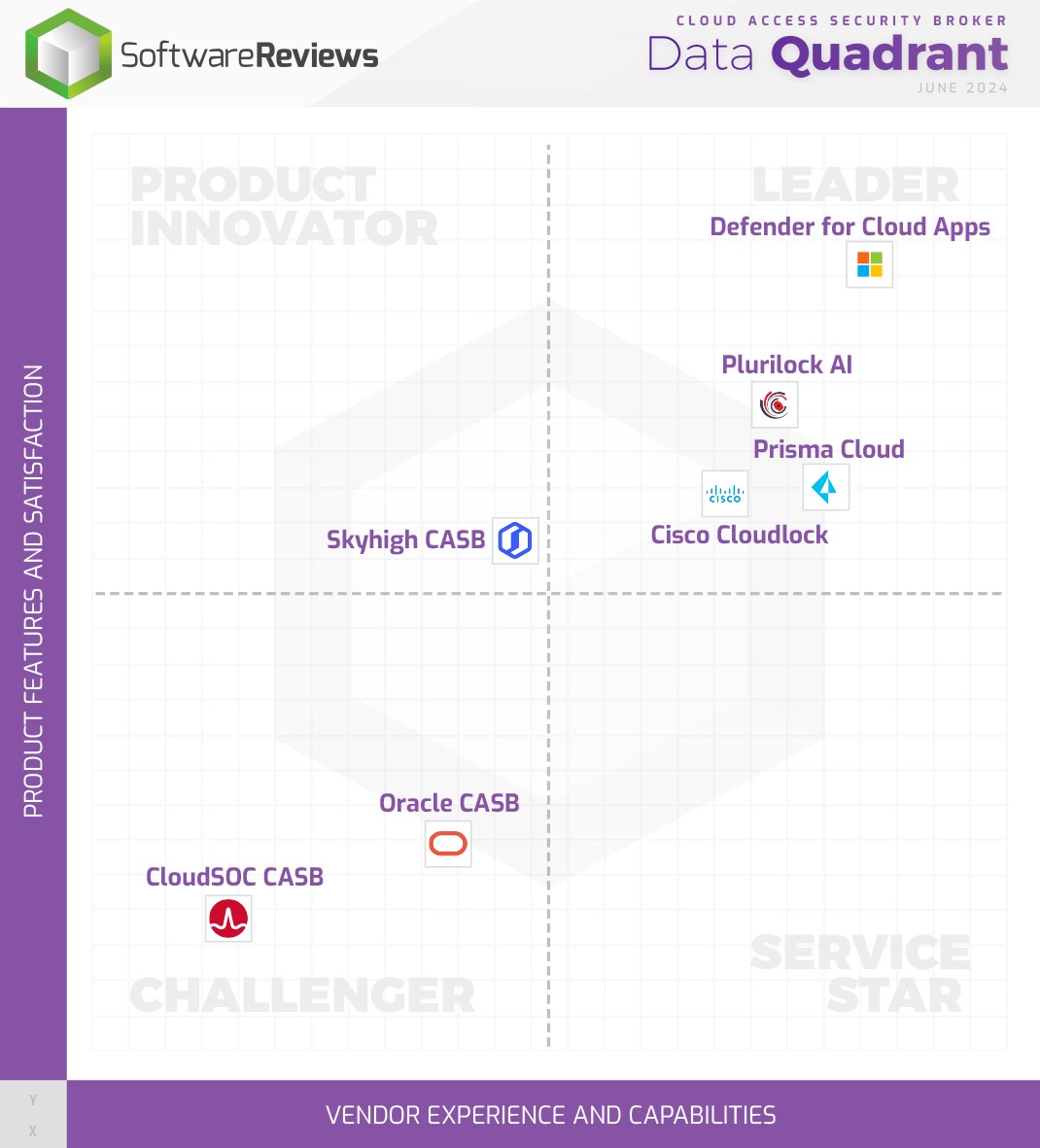
Plurilock AI is a Quadrant Gold Medalist for the Fifth Year Running
Don’t look now, but Plurilock AI has been named a quadrant gold medalist for the fifth year running by Info-Tech

Plurilock Critical Services Delivers the Capabilities You Need in a World of Increasing Risk
Data and security breaches. Regional warfare. Natural disasters. Pandemics and social crises. Supply chain instability and opacity. These are challenging


Enterprise IT and Cyber Services
Zero trust, data protection, IAM, PKI, penetration testing and offensive security, emergency support, and incident management services.

