How To comply
White House Executive Order on Cybersecurity
Last night, I signed an executive order to improve the nation’s cybersecurity. It calls for federal agencies to work more closely with the private sector to share information, strengthen cybersecurity practices, and deploy technologies that increase reliance against cyberattacks.”
— U.S. President Biden
The Colonial Pipeline
The Colonial Pipeline incident appears to be the straw that broke the camel’s back.
With global cybercrime costs reaching nearly $1 trillion in 2020 according to the Center for Strategic and International Studies, and average ransomware payments now well over $300,000 according to Palo Alto Networks, the threat level both globally and within the United States is clearly increasing.
United States President Joe Biden has issued a new executive order on cybersecurity. The costs of this alarming increase were brought home by the Colonial Pipeline attack in particular, which has led United States President Joe Biden to issue a groundbreaking executive order that lays the foundation for new cybersecurity best practices, increased communication between federal and private sectors, and new standards around cybersecurity incident handling.
Achieving Executive Order Readiness
A number of key strategies will be required to achieve readiness to comply with the executive order inspired by the Colonial Pipeline attack. Here are the four most important.
■ Adopt a Zero Trust Architecture (ZTA)
The order compels the federal government must move toward a zero trust architecture (ZTA) based on NIST standards and guidance:
“The Federal Government must...develop a plan to implement Zero Trust Architecture, which shall incorporate, as appropriate, the migration steps that the National Institute of Standards and Technology (NIST) within the Department of Commerce has outlined in standards and guidance, describe any such steps that have already been completed, identify activities that will have the most immediate security impact, and include a schedule to implement them.”
In recent years, “Zero Trust” has increasingly become a cybersecurity best practice. The term refers to a cybersecurity posture in which the network is assumed to be hostile, with no differentiation between internal and external hosts and systems. All users, both internal and external, are assumed to be threatening interlopers until proven otherwise.
Plurilock is an advanced authentication company whose cybersecurity products include Plurilock ADAPT and Plurilock DEFEND, both of which enable key forms of compliance with NIST SP 800-207.
■ Deploy Multi-factor Authentication (MFA)
The order compels agencies to adopt multi-factor authentication (MFA) to protect all data “at rest and in transit” within 180 days.
“Within 180 days of the date of this order, agencies shall adopt multi-factor authentication and encryption for data at rest and in transit, to the maximum extent consistent with Federal records laws and other applicable laws. ”
Every authentication standard and expert recommends multi-factor authentication, which combines factors that ultimately represent a combination of “something you know,” “something you have,” and “something you are.” If all three can’t be achieved, at least two should be used together.
■ Use a Cloud Access Security Broker (CASB)
The order requires agencies to move toward “secure” cloud services in a way that enables them to prevent, detect, assess, and remediate cyber incidents:
“As agencies continue to use cloud technology, they shall do so in a coordinated, deliberate way that allows the Federal Government to prevent, detect, assess, and remediate cyber incidents. To facilitate this approach, the migration to cloud technology shall adopt Zero Trust Architecture, as practicable.The Secretary of Homeland Security acting through the Director of CISA, in consultation with the Administrator of General Services acting through the Federal Risk and Authorization Management Program (FedRAMP) within the General Services Administration, shall develop security principles governing Cloud Service Providers (CSPs) for incorporation into agency modernization efforts.”
Cloud computing can turn traditional identity and security models on their head, involving multiple providers, points of risk, and points of failure. For this reason, dedicated platforms that enable cloud security, like cloud access security broker (CASB) platforms, are essential as cloud migration continues.
■ Leverage Endpoint Detection and Response (EDR)
The order requires executive branch agencies to deploy endpoint detection and response (EDR) initiatives to ensure timely detection and response:
“The Federal Government shall employ all appropriate resources and authorities to maximize the early detection of cybersecurity vulnerabilities and incidents on its networks. This approach shall include increasing the Federal Government’s visibility into and detection of cybersecurity vulnerabilities and threats to agency networks in order to bolster the Federal Government’s cybersecurity efforts. FCEB Agencies shall deploy an Endpoint Detection and Response (EDR) initiative to support proactive detection of cybersecurity incidents within Federal Government infrastructure, active cyber hunting, containment and remediation, and incident response..”
Detection and response have traditionally been among the weakest points in enterprise and Federal Government cybersecurity, with intrusions and compromises being discovered weeks, months, or even years after they occur and responses hampered by underdeveloped process and bureaucratic inertia. This needs to change.
What You’ll Need for Compliance
Order
Item
Solutions
Use
Available From
Source
Details
Info
Plurilock Security Inc. and Aurora Systems Consulting, a Plurilock company, offer a full line of cybersecurity tools, platforms, and products that can enable compliance with the recent executive order.
Plurilock offers innovative, next-generation behavioral biometrics products and services for identity and access management (IAM) and digital forensics and incident response (DFIR) purposes.
Aurora offers endpoint detection and response (EDR), email security, cloud access security broker (CASB), vulnerability management, data governance and classification, data loss prevention (DLP), incident response (IR), identity and access management (IAM), log management, managed security services, mobile security, network security and firewall, network traffic aggregation and optimization, privileged access management (PAM), and web security products and services, as well as professional cybersecurity consulting services to accelerate and enable implementation. These consulting services include application security assessments, mobile security assessments, security policy development, data loss prevention technical assessments, PCI gap analysis and compliance audit, security training, HIPAA security and compliance audit, penetration testing, security code review, cybersecurity risk assessment, phishing simulation risk assessment, and vulnerability assessments.
Refer to the table above or contact us below for details.
Let Us Help You to Comply
The Plurilock family of companies can help you to prepare for compliance with the Colonial Pipeline executive order.
President Joe Biden's infrastructure proposal calls for billions of dollars to improve cybersecurity following the Colonial Pipeline attack and the issuing of the White House executive order. It's time for organizations and agencies to move toward a more secure cyber future.
Contact us today for details.
Loading...
Thank You
We've received your inquiry and a member of our solutions team will contact you shortly.
Articles
Other Resources
Issued May 12th, 2021
Issued May 12th, 2021
Downloads
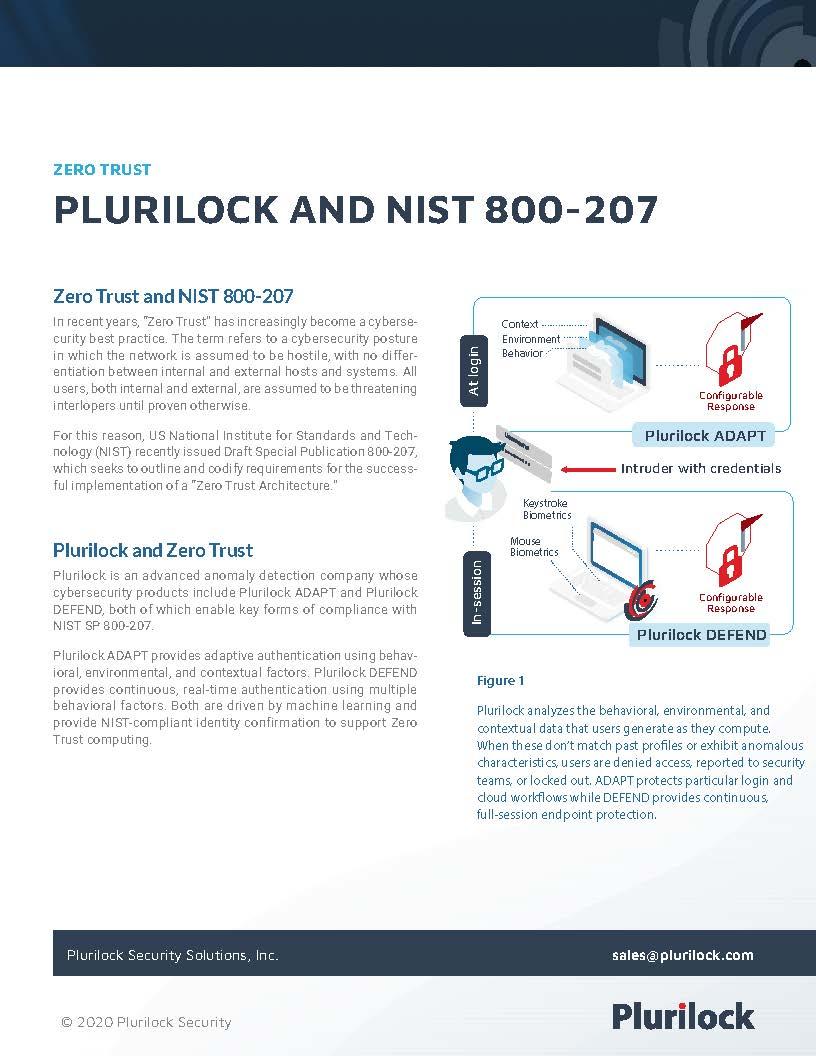
Plurilock and NIST 800-207
How Plurilock products can enable NIST 800-207 Zero Trust compliance.
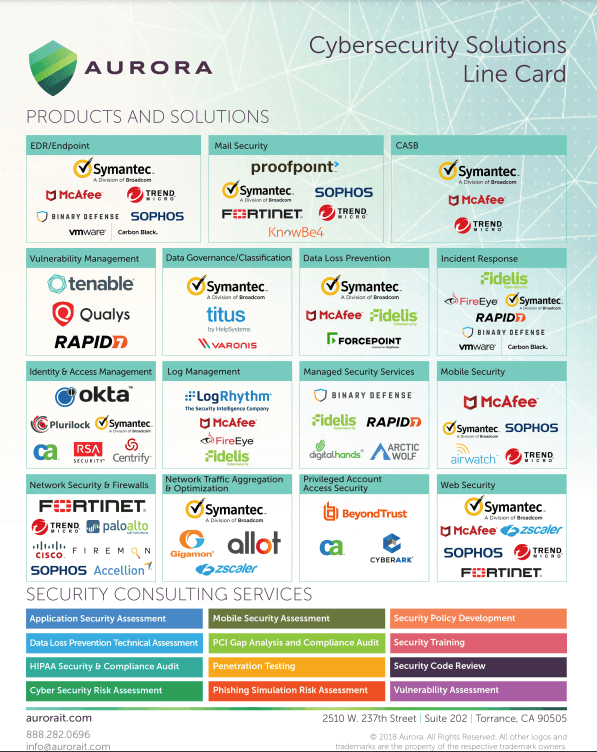
Cybersecurity Solutions Linecard
List of Aurora's solutions by category as well as consulting services they provide.




















