By now, the stat is well known.
At RSA, Microsoft reported that 99.9% of credential-driven data breaches involve accounts that weren’t protected by MFA. That’s a powerful stat—the kind of stat that has driven most CISOs to adopt MFA strategies in recent years.
Over the last few months, as workforces have rapidly transitioned to work-from-home arrangements, we’ve had a number of conversations across the industry about the state of these strategies.

And more recently, partially in response to these conversations, we’ve taken the time to survey MFA research, finding other telling statistics along the way:
-
74% of administrators say their users complain about MFA solutions
-
63% of users resist downloading and using company MFA solutions
-
60% of IT staff dislike MFA enough to avoid it in their personal lives
With figures like these, it’s no wonder that we continue to hear about the struggle to properly secure accounts with MFA.
Meanwhile, what we’ve heard from insiders more directly is that while they continue to be aware of the need for total MFA use within their organizations, significant problems remain.
Practical MFA Deployment Remains Complex and Difficult
In the real world, on-the-ground deployment of MFA remains complex, stressful, and hair-pullingly uneven.
-
Different company functions may respond to MFA solutions differently—and a solution that’s acceptable to one company function may be unworkable in another. This can lead to pitched battles or the need for multiple MFA solutions.
-
Companies are increasingly a patchwork of internal systems, cloud systems, virtualized environments, and distributed remote offices and endpoints. Though an MFA technology may be conceptually simple, rolling it out widely and successfully can prove to be an epic task.
-
Nobody likes MFA. Some are resigned to it, and others actively fight back against it—but the desire for MFA solutions that feel friendly enough to users and IT staff that they can also ultimately feel friendly to CISOs is strong.
TL;DR: Deploying MFA isn’t one task or one solution, it’s piles of both, often all in tension with each other; simpler, lower-cost MFA solutions with broader practical applicability and user compatibility are needed.
Work-from-home Makes Hardware MFA Support Harder
Providing support for passwords and password policies is time-consuming, but it can, by and large, be done remotely from regular staff accounts.

Things change, however, once companies move to hardware-based MFA solutions, particularly those that require device configuration and enrollment.
As workforces—security staff included—move offsite, new complexities are coming to the fore.
-
Hardware must be physically moved several times, between supplier and security staff, then between security staff and end user. This introduces costs, delays, and mistakes.
-
Hardware storage, deployment, and configuration isn’t easy to do in a secure and compliant way when security staff, too, are working offsite. This makes hardware-based MFA troublesome in a world trending toward offsite work.
-
Troubleshooting and support with hardware MFA introduces new complexities, terms, and approaches that can’t be reduced to managing a central identity database or doing a PC screen share—and this often slows down case resolution.
TL;DR: Hardware MFA and the move to work-from-home are in tension with one another; sound non-hardware MFA solutions are needed.
Lots of MFA Is Still Shelfware
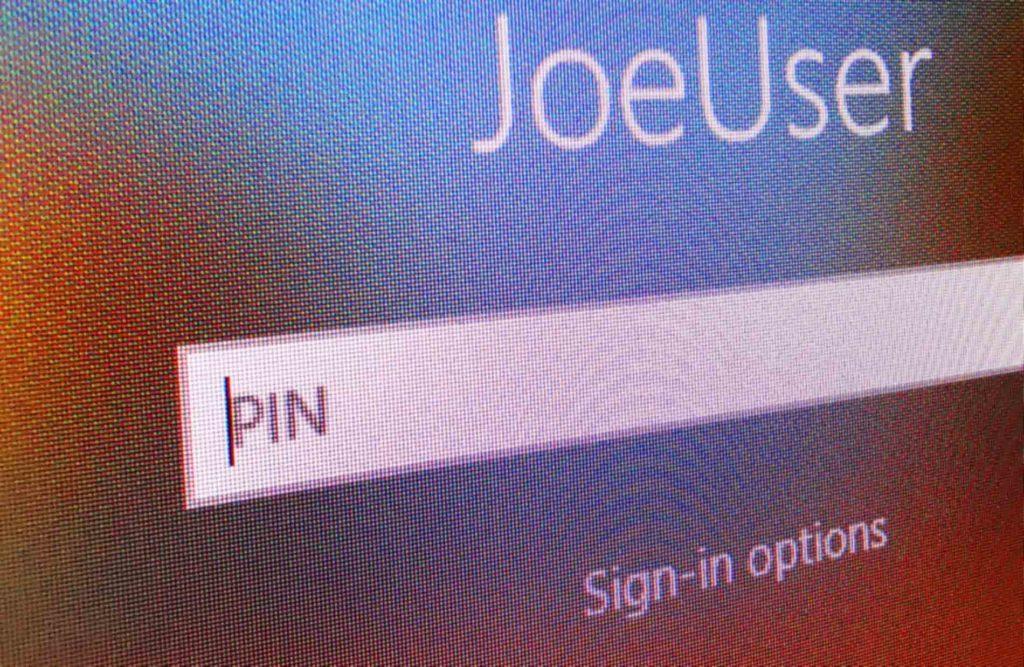
CISOs understand the importance of MFA solutions, but that doesn’t mean that new login steps or hardware are easy sells to end users.

When there are one or two users that balk at using new MFA solutions, compromises or work-arounds can usually be found. But it isn’t always one or two that are the problem.
-
In some organizations, large swaths of the workforce simply refuse to work with MFA. With large enough numbers, concerns about retention become a material concern for the business—enough to stall efforts to roll MFA out company-wide.
-
Among the common reasons for workforce reluctance are a refusal to take responsibility for, carry, and manage additional hardware and a refusal to enable corporate control of personal devices.
-
Even when security staff are in-house, managing existing MFA solutions and MFA hardware across multiple locations and departments—particularly during periods of growth and as cloud services proliferate—can be logistically overwhelming and beyond an organization’s realistic capabilities.
TL;DR: Users can find MFA onerous enough to make deployment untenable; more user-compatible and user-acceptable MFA solutions are needed.
MFA Solutions Don’t Solve BYOD Problems
As the world has moved to the cloud, much of the chatter around cybersecurity has shifted toward account protection and MFA on the end user side, and toward service and network protection on the infrastructure side. But endpoints remain a problem.

In particular, MFA is oriented toward ensuring that the right account holder is logging in to an account or service—not in ensuring that they’re using the right hardware to do so.
-
In fact, compliance requirements often demand that BYOD devices not be used to carry out a particular task.
-
Most MFA solutions do little or nothing to address this concern, leaving security staff to cobble together other solutions and constraining their choices just when maximum flexibility is needed in order to drive user adoption.
-
This becomes a particular problem as remote work proliferates and employees find ways to employ or reconfigure personal equipment for company tasks, all while authenticating properly with MFA.
-
BYOD devices and peripherals are a growing concern—these can affect compliance, and can represent attack vectors in their own right, but are currently unauthenticated. There is no simple way to authenticate not just a user and their endpoint, but also the other devices nearby or connected to it.
TL;DR: From the security perspective users aren’t singular, but are bundles of devices and services in their own right; authentication solutions that account for this are needed.
Existing Passwordless MFA Solutions Fall Short
Though there are an increasing number of “passwordless” authentication solutions on the market, some of which claim to enable multi-factor authentication without the use of traditional credentials, they aren’t always easy to embrace.
There are clear reasons why organizations are holding back on these supposedly better solutions—which don’t always manage to live up to the hype.
-
Legacy hardware is incompatible with some of the most common passwordless MFA solutions, leaving them unavailable for widespread deployment until a future hardware cycle.
-
Most of these solutions tie identity either to particular endpoint hardware, making them unworkable for many real-world situations, or to purpose-specific authentication hardware, meaning added costs and complexity and added user pushback.
-
Users that have had many years to become acclimatized to username-password flows are often either bewildered by or highly suspicious of new authentication methods.
TL;DR: Passwordless authentication sounds good, but existing solutions don’t live up to the hype; true passwordless authentication would be a game-changer.
Solving The MFA Problem
At Plurilock™, we’ve made solving these problems a key mission, providing MFA solutions that:
-
Are invisible to users
-
Require no hardware for deployment
-
Don’t add additional steps to existing login workflows
-
Relieve both support and cost load
It’s also why we think that the door remains wide open for a true passwordless solution that relieves both users and IT staff of the need to struggle when deploying authentication solutions. ■