If you’re a small business, a small organization of any kind, or an organization that lives at something of a remove from Wall Street and the hi-tech economy, cybersecurity can be an uncomfortable topic to hear about.
The experts in media report on breaches, say that business should protect themselves, and suggest that computing and the Internet are areas fraught with risk. And they are!
But what to do about it? For the average small business owner, it often isn’t clear just what “protect yourself” means, and while there are a few cybersecurity product categories that are probably familiar (notably “antivirus” software), many more of the categories and brands are jargon-heavy and can seem insurmountable, with prices to match.
Is cybersecurity beyond the reach of the average small business? Should you just buy Avast, or AVG, or Kaspersky and be done with it, while keeping your fingers crossed?
No. In fact, cybersecurity is emphatically not beyond the reach of small business, it’s just that as a society and as an industry we do a relatively poor job of communicating about it. So let’s start to fix that.
Here are seven key things that you can do without spending enterprise-level money on the project. Do these seven things, and you will have a fairly robust cybersecurity profile that any small business should be proud of.

No Cost: Sound Password and Login Practices
Often lost in the breathless news coverage—and in the chats with Facebook friends about the fact that they were “hacked” yesterday—is the fact that well over three-fourths of all cybersecurity breaches and incidents, including most email and Facebook “hacks,” are simply impersonations.
Someone with ill intent gets ahold of your password and simply logs in as you or one of your employees, then changes the password once they’re in (so that you can’t get in), and begins to use your account(s) to do whatever they please.
There are a variety of ways for passwords to fall into the wrong hands, but almost all of the negative effects can be stopped with a few simple practices that you should implement at your business right away:
-
Instruct or require all employees to use strong passwords. A strong password is a password that’s virtually impossible to guess. This means that passwords like “Password123” or birth dates or spouse names or “ZachsMom13” are out. Yes, it can mean a password that makes everyone groan, like “Zy3X!*v^9Qm” but it can also mean something easier to remember like “DogFlowerOatGrub” that has multiple words that aren’t related in any way to the user in question.
-
Instruct or require all employees to use a different password for each account. Password re-use is a significant cause of cybersecurity compromises. That is to say that when a user uses the same email address and password for 20 different accounts, only one password has to be stolen for an attacker to gain access to all 20 accounts. If a different password is required for every account, the “footprint” of an attack is much smaller.
-
Instruct or require regular password rotation. Many attacks begin when entire batches of login details, revealed in a previous data breach, are purchased by an attacker on the dark web. These batches can thousands of accounts long—and it can take time for an attacker to “get around to” taking over any one account. Changing passwords several times a year increases the chance that by the time an attacker gets around to trying out a particular password, it’s no longer current.
-
Enable two-factor (2FA) or multi-factor authentication (MFA) everywhere you can. Most major online platforms these days—Amazon, Google, eBay, Microsoft, and so on—provide a free option for 2FA. These are those codes that some sites send to your phone, or that you see in an app, and that you must then enter in order to log in. These codes aren’t magic, they’re just a number that changes every few seconds that needs to match what’s expected for a login to work. They make it so that an attacker needs your phone, in addition to your password, to steal your account.
Let’s repeat what we said earlier—by observing these four simple rules, you can eliminate around three-fourths of the cybersecurity risk for your small business. They are the bedrock of cybersecurity.
Now it can be difficult for even the best-intentioned small business to execute on these, so if that sounds like you—if you’re looking at the list above and groaning—there is a pretty good shortcut that covers most of them.
Give your employees a password manager like 1Password or LastPass. These are simple programs that just store passwords for accounts. In order for a user to access their passwords, they need to enter a “master password” that unlocks their list of passwords.
With a password manager, there’s no longer much in the way of excuse or hesitation around using long, strong passwords, or a different password for each account, because employees don’t have to remember them all. The software does this for them. Just ensure that the master passwords that each employee uses (the one that safeguards all their other passwords) is long and strong.

No Cost: Data Backups
For many (though certainly not all) smaller businesses the biggest risk and potential cost involved in a cybersecurity breach is loss of data. All the stuff you were working on. All the files you’ve accumulated.
Ransomware attacks leverage this fact to get business owners to pay up—they realize that without its data, a business is simply unable to continue to operate, so a business will often happily pay up to get access to their data again.
You can short-circuit this leverage simply by having backups. A full list of the ways in which backups can be maintained is beyond the scope of this article, but it can include any one or several of:
-
Regularly copying data to an external hard drive. These days external storage that connects over USB is inexpensive, and many small offices even have a few external storage devices laying around. Put them to use. Just be sure to (a) back up files regularly, so that backups aren’t out of date enough to be useless and (b) disconnect these devices after data is copied, so that a ransomware attack doesn’t lock up all their data, too.
-
Using a network or cloud backup service or device. These days there are a good number of cloud backup services and network backup devices. Making a comprehensive list is beyond the scope of an article like this one, but it’s possible that you have access to significant cloud storage and don’t even realize it. Look into whether there is any cloud storage offered by your internet service provider, and whether you have significant cloud storage available to you through Microsoft or Google if you use their applications. Then, just drag and drop important files to the cloud.
-
Using cloud versions of applications. If you’ve been around the block a few times, it can be hard to move to using software in a browser, instead of using the “standalone app” version. The cloud versions, however, have a key benefit—they store your files in the cloud, i.e. at Google or at Microsoft and so on, and those organizations are much better-positioned to run a major cybersecurity organization and keep data safe and available.
The key point here is to put your data somewhere where it won’t disappear or be locked up for ransom in the case of an attack. Whether this is on an external backup device, on a cloud storage service, or just in cloud versions of applications is up to you—any of them will ensure that your data is available to you if someone manages to compromise and damage your computing environment.

No Cost: Update Policies
The next major cause of data breaches is poor update hygiene. Yes, all those software and firmware updates that are running all the time have a purpose beyond delivering you new features.
Though they’re less common, there are hackers out there that specialize in performing highly technical attacks on software in which flaws have been discovered.
These days, virtually all software and firmware is complex enough that it will have flaws. As these are discovered or reported to software makers, they fix the flaws and release new versions—that arrive via software updates.
Here’s the thing—once a flaw has been discovered or reported, news of the flaw spreads like wildfire, and the first thing these attackers do is head out in search of victims using the flawed versions software or the devices in question.
So ensure that all of your devices and programs have auto-update enabled so that updates are received and installed as soon as they’re known—and set up a frequent cadence (weekly is a good default) to visit the manufacturer websites for anything without auto-update capability to see if new versions have been released.
Keep everything up to date and you’ve eliminated another important cause of cybersecurity breaches.
No Cost: Make an Incident Plan
If you haven’t already done so, take time to plan out what you will do if you or one of your employees, or a company system, is breached.
Smaller organizations often don’t think about this beforehand, but it’s a lot easier to operate according to an existing plan than to try to come up with one in the heat of a panic moment.
The plan should cover:
-
Who should be notified internally of a suspected compromise or breach
-
Which systems or accounts should be checked or disabled
-
Who the potential affected parties (customers, partners, etc.) are
-
How they should be notified and under what conditions
-
Which law enforcement agencies to contact
-
Which service provider(s) to contact in case help is needed
-
How normal operation will be restored once checks and remediation are complete
This plan can very in complexity from organization to organization, but having all the steps, phone numbers, and responsible names in one place can help to avoid making a chaotic situation worse if the worst happens.

No Cost: Basic User Training
One thing that’s often neglected in and around the practices above is user training. For a small business, this doesn’t have to be excessively complicated—but it needs to be done.
Gather your employees once a month, or whenever someone new is hired, and:
-
Go over the password and login rules above. Reiterate to your employees the importance of strong passwords that aren’t easy to guess, and of using a different password on every account. If you’ve assigned them a password manager tool, check in with them—is it being used, or do they need help?
-
Remind them of data backup and update policies. In the case of data backups, if you’re having employees back up their own files, this reminds them to do it. If you’re managing backups yourself, this helps to encourage them not to store personal data on company computers. In the case of update policies, this provides a forum for them to notify you if they haven’t seen any updates running in a while—so that you can get to the bottom of things for their software or hardware and ensure that they’re running latest versions.
-
Go over the plan. Refresh everyone’s memory of your incident response plan, make sure that all of the information is still current, and that everyone understands what the steps mean, how to act on them, and when or under what conditions they should ask you if it’s time to put the plan into action.
This discussion also provides a forum for you to approach other cybersecurity topics that are often forgotten by smaller organization, such as rules and policies around which data can or can not be shared, and with whom, as well as rules and policies around who is allowed to access company devices or accounts and when.
Affordable: Anti-malware Tools
Yes, that anti-malware software you paid for does have a place in this list!
Since small businesses and smaller organizations outside the tech economy often don’t have the horsepower or expertise to run heavier cybersecurity tools that police what happens on every computer and make sure they are secure, anti-malware software is the go-to for small businesses, to ensure that unwanted, malicious software isn’t present or inadvertently added.
Just be sure to enable those automatic updates so that the anti-malware tools can check your systems for the latest threats as they are discovered.
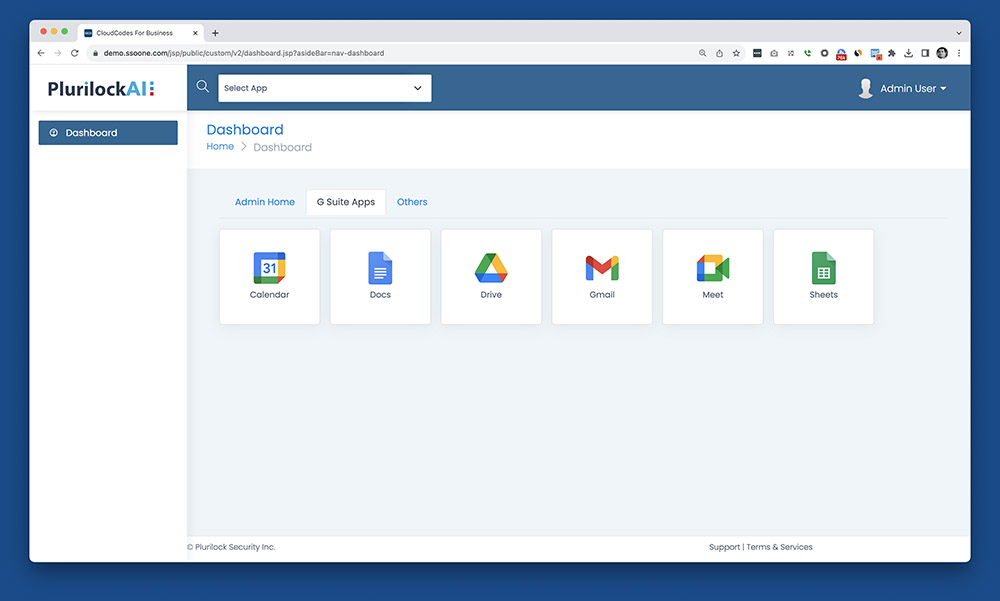
Affordable: Plurilock AI
When you’ve addressed all of the above and are ready to get into more advanced cybersecurity tooling, fear not—there are more serious cybersecurity platforms that are affordable to small businesses.
Plurilock offers Plurilock AI DLP, which provides a number of capabilities that go well beyond anything outlined above:
-
Single sign-on (SSO). This enables your employees to log in once to the single sign-on provider, then see a dashboard of their other accounts. They log into any of these other accounts just by clicking on it—the single sign-on platform logs into the third party for them, securely. You also gain control over where, when, and with what device(s) users can log into their accounts.
-
Cloud access security broker (CASB). This enables you to centrally control how files and data in cloud applications like Google Workspace (Docs, Sheets, Slides) and Microsoft 365 can be accessed, modified, and shared. You make the rules and they are enforced for all of your employees and anyone they plan to share data with.
-
Data loss prevention (DLP). This enables you to control how data flows around, in to, and out of your company. You’ll gain control over copy-paste functions, whether USB flash drives can be used, what can be downloaded and uploaded, even whether personal accounts can be used from company devices, to prevent data from inadvertently making its way out of your company and into the wrong hands.
Plurilock AI offers the heavy-hitting cybersecurity functionality that much larger organizations rely on, but offers price points and levels of customer service that’s much more palatable to small businesses, not just enterprises.
If you’re serious about cybersecurity at your business, find out more about Plurilock AI and try it out in your organization.
Stretch Goal: Hire an MSP or MSSP
When you’re ready to grow, consider hiring a managed service provider (MSP) or a managed security service provider (MSSP).
As a small business owner it’s up to you to decide when the time is right for a step like this. It will generally cost more than the other steps here, but it will put your business security in the hands of an expert that caters to businesses like yours, enabling you to double-down on your success and spend your time focusing on your business—while others focus on your security.
If you think you may be at this stage, get in touch sooner rather than later, as service provision isn’t necessarily and all-or-nothing thing. You may find that there are some areas in which it’s cost-effective for them to take over, and some areas in which—for now—you want to continue to manage things yourself.
You Can Be More Secure Than You Think
Rather than imagining that your small business is a target with little protection in a big and dangerous world, then hoping for the best, survey the steps above, put together an action plan, and make them happen.
By covering the majority of items above, you’ll put yourself in a very secure position relative to other businesses around the world—not just the small ones, but even some of the larger ones, too. ■