Internal actors are implicated in more than a third of recent data breaches.
If you're an IT or security professional in the corporate world, that's an alarming statistic. And yet for many corporate cyberattack victims, catching and excluding internal bad actors is an increasingly difficult task. Why?
Because in too many organizations today, there is no necessary relationship between users and their authentication credentials—no way to prove that when a particular set of credentials was used, a specific person was using them.
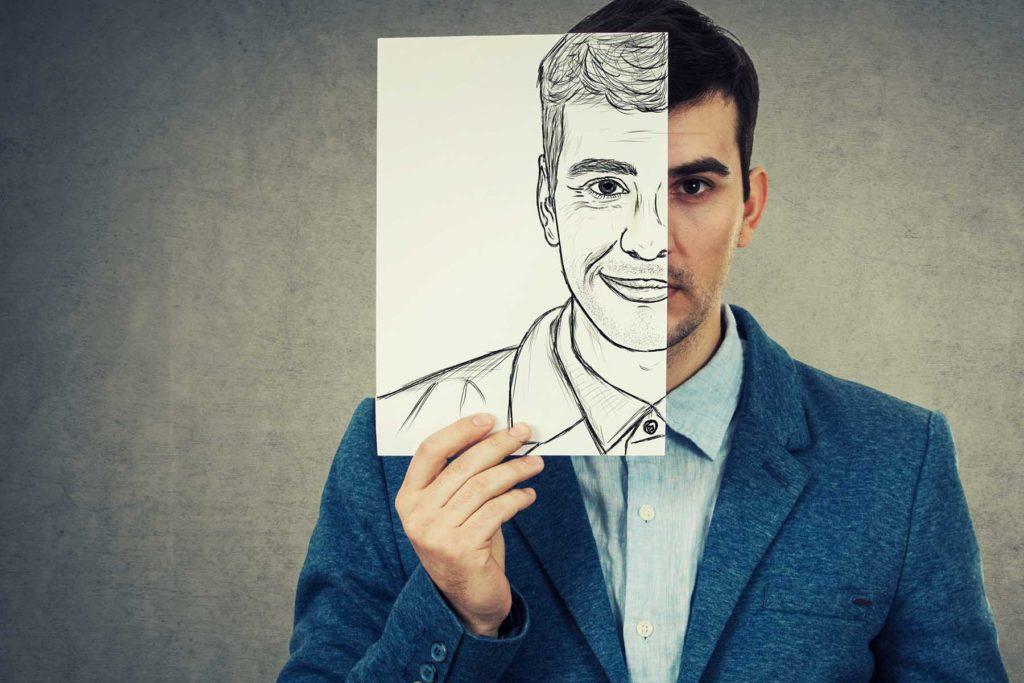
As a result, once company accounts or systems have been compromised, it's easy for an internal bad actor to "blend in" with the background—to say that:
-
“I have no idea how this happened.”
-
“They may be my credentials, but I wasn’t the one using them at the time.”
-
“Since our credentials have been compromised, evidently the attackers were using mine!”
Worse, the more common cybersecurity incidents and data breaches become, the more plausible this defense becomes. After all, there are over three quarters of a billion sets of valid credentials in the wild already.
Non-repudiation Strategies are Needed
What's needed is a way to definitively know who's responsible for activity carried out using a given set of login credentials. In other words, what's needed is a way to prove that:
-
A particular attack—
-
was carried out using a particular set of credentials—
-
that were demonstrably in use by a particular individual—
-
who is the responsible party.
At present, most companies can forensically demonstrate the first, second, and fourth bullets above—but not the third.
Unfortunately, it's the third bullet that matters most, enabling administrators to take clear action and ensure that the person responsible for a past breach won't have the access to initiate a future one.
Furthermore, the ability to prove that a particular person is responsible for a data retrieval, transmission, or modification event is often operationally, legally, and ethically important even in the absence of a breach event.

This is true in a variety of industries, including:
-
Healthcare
-
Financial services and banking
-
Education
-
Critical infrastructure
-
Government and military work
So, given the growing importance of non-repudiation capability, what strategies exist for achieving it? Let's take a look.
Methods for Achieving Non-repudiation Capability
At the moment, only biometric forms of authentication can claim to tie a particular real-world individual to a particular computing session.
Every other kind of login authentication—username and password, hardware token, SMS code delivered by phone, access card, and so on—proves only that someone had the credentials to log in, rather than confirming just who that someone was.
Within the realm of biometrics, however, there are a range of possible choices in non-repudiation solutions, each with a particular level of non-repudiation certainty:
-
Weakest: Biometric authentication with fingerprint or face scans
-
Stronger: Behavioral-biometric authentication at login
-
Strongest: Continuous authentication using behavioral biometrics
Traditional biometric authentication is the weakest. It links a computing session to a real person only at login, after which claims of session theft and step-aways remain plausible. Worse, fingerprint and face scan solutions are known to be vulnerable in a variety of ways, significantly compromising them as non-repudiation technologies—for the very same reasons outlined above.
Behavioral-biometric authentication at login is somewhat stronger. Biometric data of this kind is far less vulnerable to impersonation, theft, or reuse—a big plus. Unfortunately, when used only at login, behavioral biometrics again leaves the door open for claims of session theft either via technical means or as the result of an inadvertent walk-away.

Continuous behavioral-biometric authentication is currently the best non-repudiation option available. It relies on behavioral-biometric data that makes impersonation, theft, and reuse difficult or impossible while at the same verifying identity continuously as work happens—thus preventing claims of session theft or compromise due to inadvertent walk-aways.
Choosing a Non-repudiation Solution
Though this discussion is probably new to some, for many organizations the problem isn't so much a matter of understanding non-repudiation needs, benefits, and technologies as it is finding a solution that's practical—one that's shipping, affordable, and compatible with organizational needs and infrastructure.
At Plurilock™, of course, we offer both login-based and continuous behavioral-biometric solutions for non-repudiation, via our ADAPT and DEFEND products, respectively, and are able to support most cloud applications as well as ADFS, Mac OS, and Windows environments.
But whichever provider(s) your organization selects, given the points outlined above, we’d advise companies that are seeking non-repudiation capability to identify and consider solutions that:
-
Rely on behavioral biometrics for authentication
-
Perform this authentication continuously, at all times as work happens
Solutions that meet these two points enable truly strong non-repudiation capability.
They eliminate the "It wasn't me!" problem in cybersecurity, so that internal bad actors can be clearly identified—and their access to cause future havoc and harm can be ended. ■