Ransomware in Cybersecurity: A Deep Dive
In recent years, ransomware has emerged as one of the most pervasive and destructive threats in the field of cybersecurity. This malicious software, which encrypts a victim’s data and demands a ransom for its decryption, has caused significant financial losses and operational disruptions across various sectors. This deep dive explores what ransomware is, why it matters, and provides in-depth analysis of its importance in the ever-evolving landscape of cybersecurity.
Understanding Ransomware
1.1 What is Ransomware?
Ransomware is a type of malicious software (malware) designed to encrypt a victim’s data and demand a ransom from the victim in exchange for the decryption key. Once infected, victims typically find their files and data inaccessible, rendering their systems unusable. Ransomware can affect individuals, businesses, and even government organizations, causing a wide range of consequences, from financial losses to reputational damage.
1.2 How Ransomware Works
Ransomware operates by exploiting vulnerabilities in computer systems, often through phishing emails or malicious downloads. Once it infiltrates a system, it encrypts files using a strong encryption algorithm, making it nearly impossible to decrypt the data without the attacker’s private key. After encryption, victims receive a ransom note that provides instructions on how to pay the ransom, usually in cryptocurrency like Bitcoin.
1.3 Evolution of Ransomware
Ransomware has evolved significantly since its inception. Early versions were relatively simple and easily circumvented by security experts. However, modern ransomware employs advanced techniques, such as polymorphic code (which changes its appearance to evade detection) and sophisticated command-and-control infrastructure. Ransomware developers have also embraced ransomware-as-a-service (RaaS) models, allowing less technically proficient criminals to use ransomware for profit.
Why Ransomware Matters
2.1 Financial Impact
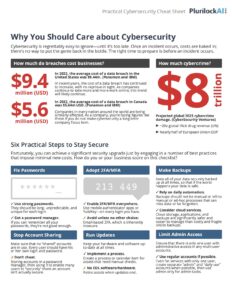
Ransomware attacks often result in substantial financial losses. Victims not only face the ransom payment but also the costs associated with downtime, data recovery, and system restoration. In 2020, the average ransom demand exceeded $170,000, according to cybersecurity firm Coveware. Moreover, the indirect costs, such as damage to reputation and customer trust, can be even more devastating.
2.2 Operational Disruption
The operational disruption caused by ransomware attacks can be crippling. Organizations may experience downtime ranging from days to weeks, leading to a significant drop in productivity. Critical services may be interrupted, impacting not only the organization but potentially the public as well. Hospitals, for example, have been targeted, endangering patient care and safety.
2.3 Data Loss and Privacy Concerns
In addition to financial losses and operational disruptions, ransomware attacks often result in data loss. Some attackers threaten to release stolen data if the ransom is not paid, putting sensitive information at risk. This raises concerns about data privacy and regulatory compliance, as organizations may be legally obligated to report data breaches.
2.4 Ransom Payments
Paying the ransom is a contentious issue. Some organizations choose to pay in desperation to regain access to their data and systems quickly. However, this practice has its drawbacks. It encourages cybercriminals to continue their activities, funds future attacks, and provides no guarantee that victims will receive a decryption key. Additionally, paying the ransom may violate legal and ethical principles.
In-Depth Analysis of Ransomware’s Importance
3.1 Disruption of Critical Infrastructure
One of the most critical aspects of ransomware’s importance in cybersecurity is its potential to disrupt critical infrastructure. Attacks on sectors such as energy, transportation, and healthcare have the potential to cause widespread chaos and even threaten public safety. For instance, the Colonial Pipeline ransomware attack in 2021 resulted in fuel shortages and demonstrated how a cyberattack on essential infrastructure can have far-reaching consequences.
3.2 Economic Impact
Ransomware attacks can have a profound impact on the economy. The costs associated with these attacks, from ransoms paid to recovery efforts, can be substantial. Moreover, the threat of ransomware can deter investment and innovation, as businesses fear the financial repercussions of potential attacks. This, in turn, can hinder economic growth.
3.3 Cybersecurity Arms Race
The rise of ransomware has sparked an ongoing cybersecurity arms race. Cybercriminals continuously adapt and develop new techniques to evade detection and improve their ransomware campaigns. In response, cybersecurity professionals and researchers work tirelessly to develop countermeasures and security solutions. This ongoing battle underscores the importance of staying ahead of cyber threats and the constant need for innovation in cybersecurity.
3.4 Impact on Trust
Ransomware attacks erode trust in digital systems and services. When individuals and organizations can no longer rely on the security of their data and systems, they may become hesitant to adopt new technologies or fully embrace digital transformation. This skepticism can hinder technological progress and limit the potential benefits of the digital age.
3.5 International and Political Ramifications
Ransomware attacks often transcend national borders, with cybercriminals operating from jurisdictions that provide safe havens. This complexity raises international and political ramifications, as governments grapple with how to address cyber threats effectively. Diplomatic tensions can arise when attacks are linked to state-sponsored actors, highlighting the need for international cooperation in addressing ransomware and other cyber threats.
3.6 The Human Element
While technological advancements and vulnerabilities play a significant role in ransomware attacks, the human element is equally important. Phishing emails, social engineering, and insider threats are common entry points for ransomware. Educating individuals and employees about cybersecurity best practices and promoting a culture of security awareness within organizations is crucial to mitigating these threats.
Mitigating Ransomware Threats
4.1 Robust Cybersecurity Practices
Effective cybersecurity practices are essential for mitigating ransomware threats. This includes regularly updating and patching systems, implementing robust access controls, and conducting security training and awareness programs. Multi-factor authentication (MFA) and endpoint detection and response (EDR) solutions can also help prevent and detect ransomware infections.
4.2 Backup and Recovery Strategies
Regular data backups are crucial for recovering from ransomware attacks without paying the ransom. Organizations should maintain offline backups of critical data and test their recovery processes to ensure they can quickly restore systems and minimize downtime.
4.3 Zero Trust Architecture
Adopting a zero trust architecture, which assumes that threats can exist both inside and outside an organization’s network, can enhance security. By continuously verifying user and device trust, organizations can reduce the attack surface and limit the impact of ransomware.
4.4 Threat Intelligence and Sharing
Sharing threat intelligence within and across industries can help organizations better prepare for ransomware attacks. Collaborative efforts can lead to the early detection of new threats and the development of effective countermeasures.
4.5 Legal and Regulatory Measures
Governments and regulatory bodies play a critical role in addressing ransomware. Legislation and regulations that impose penalties on ransom payments and require organizations to report breaches can discourage ransomware activities. However, striking a balance between deterring cybercriminals and protecting victims’ interests remains a complex challenge.
Conclusion
Ransomware has become a pervasive and highly destructive force in the realm of cybersecurity. Its ability to disrupt critical infrastructure, cause financial losses, and erode trust in digital systems underscores its importance. Addressing the ransomware threat requires a multifaceted approach that combines robust cybersecurity practices, technological solutions, international cooperation, and legal measures. As the cyber landscape continues to evolve, staying vigilant and proactive in the fight against ransomware remains a paramount concern for individuals, organizations, and governments alike.