Key Points
- With more (and more expensive) cybersecurity systems in place than ever, alert load is through the roof
- Most of the alerts a SOC team member will triage on any given day are false alarms
- This unsustainable load means both complacency and burnout in overworked SOC teams
- It also means that real threats are inevitably missed, defeating the purpose of the alerts
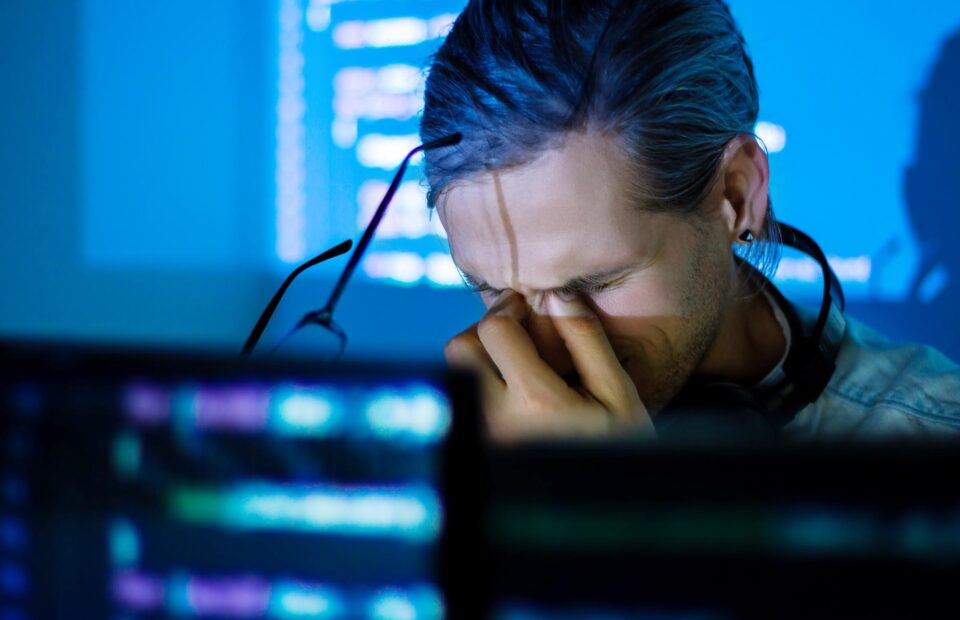
SOC alert load is growing at an alarming pace, and of course the vast majority of alerts are false alarms. With expensive systems constantly crying wolf, dangerous consequences and burnout are inevitable.
Quick Read
As cyber threats and breaches become bigger and bigger concerns for organizations of all kinds, the list of cybersecurity systems and tools has grown rapidly in recent years. Each of these systems and tools comes with its own list of red flags—alert conditions—that "may indicate" that a breach has occurred.
Unfortunately, most of these systems and tools rely on inference and correlation for their alert conditions. Rather than alerts that mean "you have been breached, remediate now" they instead generate alerts that can mean any combination of "possible breach," "possible bad behavior," "possible new risk," "please investigate," or even "hmm, take a look when you can."
In short, as designed these systems generally flag anomalies—cases of odd, suspicious, or unusual circumstances—with the expectation that a human cybersecurity team member will follow up and find out "what's really going on." This isn't a design flaw per se; most cybersecurity systems simply don't have enough intelligence or data about the real world to be certain of what's "really going on, big picture"—only that something seemingly unusual is happening.
While these alerts are well-intentioned, and often wanted by the teams that deploy them, the presence of many such systems means the generation of many, many alerts—the vast majority of which will turn out to be false alarms.
Ponemon estimates that the average organization sees nearly 17,000 alerts per week. Doing the math, this works out to essentially two alerts every minute of every day, twenty-four hours per day, in perpetuity—with the alert rate growing at a double-digit rate, year over year. Very few organizations have large enough teams to properly investigate alerts that arrive in this kind of deluge, and indeed Ponemon estimates that fewer than 1 in 20 alerts are ever investigated at all.
Instead, practically speaking, team members tend to develop habits that amount to ignoring the vast majority of alerts. This both nullifies the benefits provided by many cybersecurity systems and tools and ensures that over time, some "real" alarms will also be ignored, often with catastrophic consequences—a breach right in the middle of what were presumed to be an organization's strongest cybersecurity defenses.
To solve this problem, companies need to ensure that they shift some of their focus away from acquiring still more tools to "protect" and "alert" and instead acquiring tools to "understand" and "investigate." Organizations should deploy security information and event management (SIEM) and security orchestration, automation and response (SOAR), then configure and integrate them carefully to to enable these systems to "automatically investigate and act on" alerts when possible—to relieve human team members of alert triage load.
To enable as much automation as possible, organizations should also look to solutions that provide enrichment data for SIEM/SOAR like Plurilock DEFEND. This focus on adopting systems to gather intelligence, rather than systems to actively protect and alert, is a culture shift for many organizations—but automatically gathering this intelligence and then providing it to well-configured SIEM/SOAR systems, rather than simply alerting on it, is the only pathway out of the alert fatigue forest.
Further Reading
 Need Alert Fatigue solutions?
Need Alert Fatigue solutions?
We can help!
Plurilock offers a full line of industry-leading cybersecurity, technology, and services solutions for business and government.
Talk to us today.
Thanks for reaching out! A Plurilock representative will contact you shortly.
What Plurilock Offers
More to Know

Too Many Sirens
An alert condition is meant to be like a police siren—commanding the attention of cybersecurity teams. But when there are thousands and thousands of alerts per day, teams learn to ignore the sirens and just carry on on autopilot.

Human Factors in Cybersecurity
The "human information overload" problem that has long been an area of focus and concern in certain other industries has arrived in cybersecurity, but organizations and experts are still coming to terms with this reality. The reduction of alert fatigue must be a key goal for cybersecurity going forward.