Key Points
- These solutions authenticate users without requiring user input or specific steps carried out by the user
- They generally operate in the background, and in some cases can operate continuously (i.e. at all times)
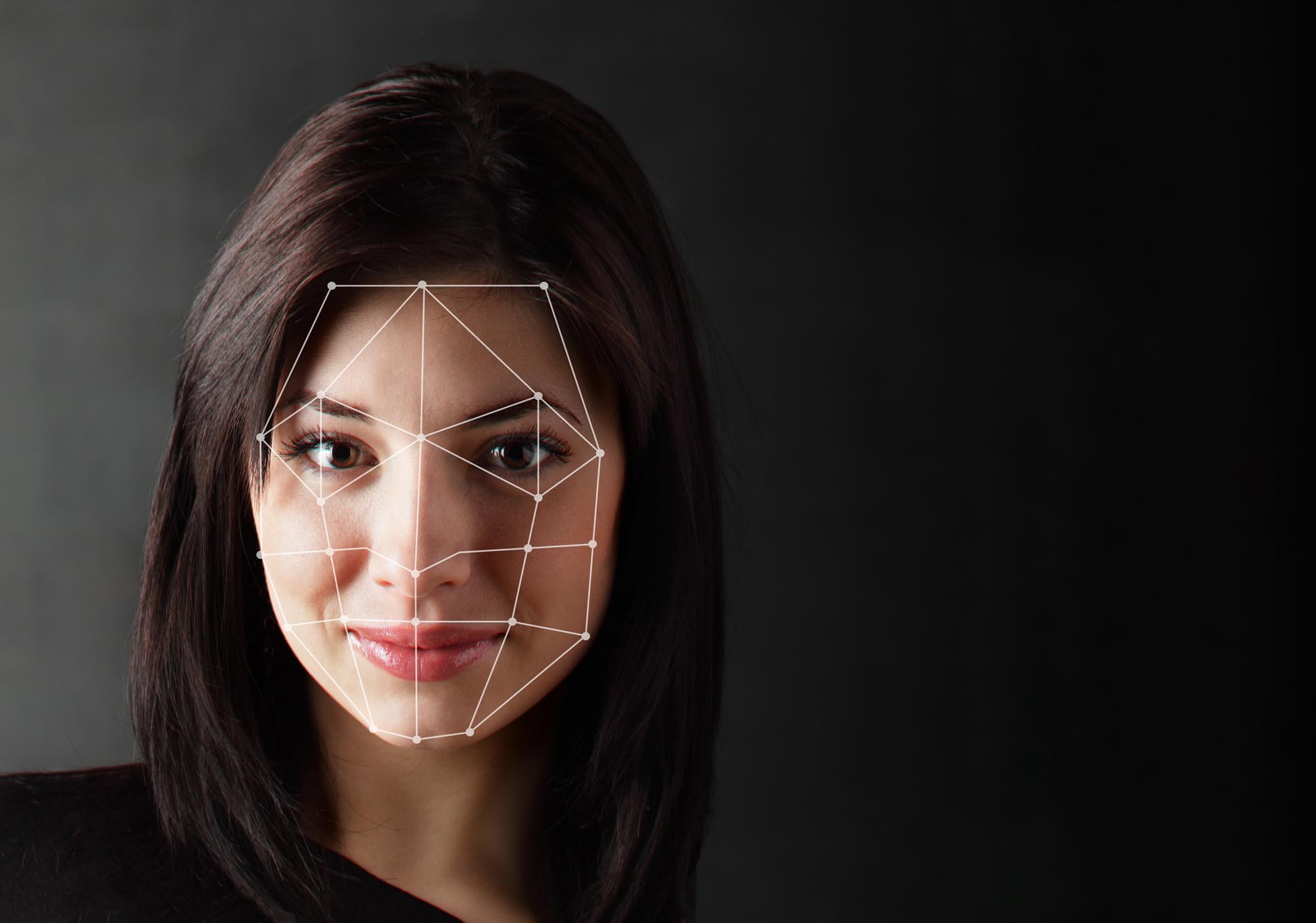
- Behavioral biometrics and facial recognition using a laptop webcam are common examples of passive authentication
- Passive authentication is one solution to the ever-growing problem of too many authentications per day or per workflow

The sheer number of authentications required of users today can lead to frustration and loss of productivity. Passive authentication is meant to solve this.
Quick Read
As technology—and especially the cloud—become more and more a way of life, authentication has come to take up more and more of the average person's time. This is true both in the lives of employees and in peoples' private lives after hours.
Sometimes it seems as though getting anything done is an endless set of authentication steps, so that it takes minutes or even hours to get started on nearly any task as you try to complete all of the authentications needed to start all of the software needed to begin.
Passive authentication is one possible answer to this problem.
The goal of passive authentication is to find a way to confirm identity—and thus a way to ensure secure computing—that doesn't require the user to take any particular concrete steps. Examples of passive authentication include technologies like behavioral biometrics and some forms of camera-based face identification (for example, when positioned above a laptop screen).
These technologies can simply "look at" the user and decide whether or not they should be authenticated—without the user having to stop and type things in, look things up, place a finger somewhere, provide a code, or do anything else that takes time. Instead, authentication happens (for the user) in a "passive" way.
Because it takes time to do all of these things, passive authentication is generally a way to accelerate all of the authentication steps that a user would otherwise have to perform, reducing the total time they dedicate to authentication from minutes or hours down to seconds, and also a way to eliminate friction that might ultimately negatively affect a user's work, or perceptions of the software, or that might even cause them to give up on beginning a task at all.
Further Reading
 Need Passive Authentication solutions?
Need Passive Authentication solutions?
We can help!
Plurilock offers a full line of industry-leading cybersecurity, technology, and services solutions for business and government.
Talk to us today.
Thanks for reaching out! A Plurilock representative will contact you shortly.
What Plurilock Offers
More to Know

Too Much Authentication
Most users and employees would agree that there's too much authentication in the world today. There's so much authentication that sometimes it feels difficult to get any work done.

No Interruptions
Passive authentication enables systems and software to identify users as users go about their business, without users having to perform "authentication steps."